Category: IOT/OSINT/SCADA
Points: 300
Description:
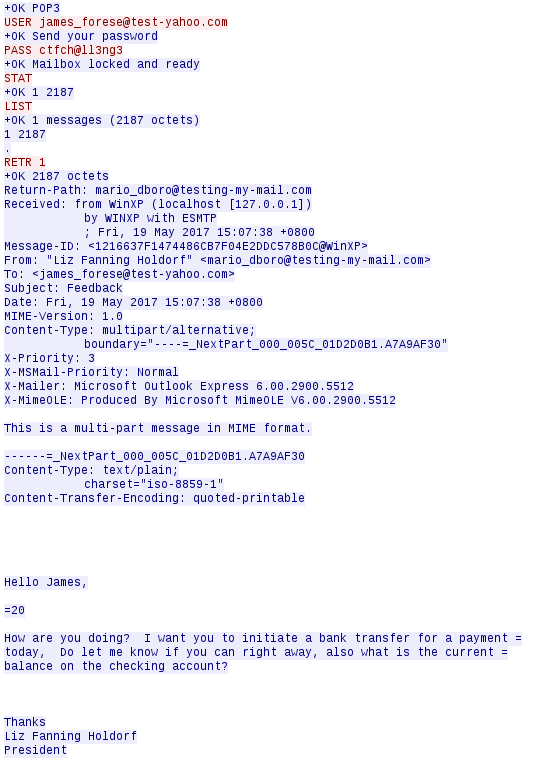
Within the ICS enviroment there has been some odd behavior with one of the network switches. You have asked your Network Administrators to see if they could pull some traffic from their packet capture solution. They dug into the issue and couldn't make sense of whats going on but think that there may be an attacker that has figured out a backdoor into the system based off an SSH connection.
Figure out how the attacker was able to exploit the system, and utilize the backdoor to SSH into the system
To submit the flag, you'll have to wrap the backdoor into TMCTF{}
Download the file (https://s3-ap-northeast-1.amazonaws.com/trendmicro-ctf-2017/2VjxmQSdV3uBQvReFLea/files19.enc)
Decrypt the downloaded file by the following command.
> openssl enc -d -aes-256-cbc -k lnlzeirDTOWxKBdpBTsz -in files19.enc -out files19.zip
> unzip files19.zip
Investigation
Once we’ve got a pcap, I got started by exporting http objects in wireshark. One thing I noticed in the http streams is a file named exploit.tar.gz. Let’s look at that conversation and export the data as raw from wireshark.
Once we’ve extracted that, we can run tar zxvf exploit.tar.gz and one of the more interesting files that popped out was /etc/passwd
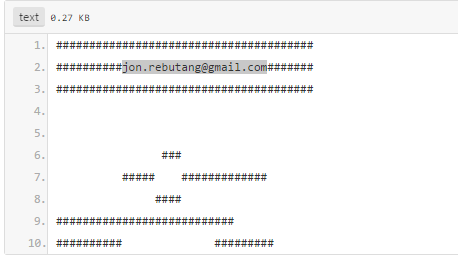
The obvious thing that stands out in /etc/passwd is this line:
TMCTF:MFzbJnLcqzlvo:0:0:Hold the backdoor:/home/admin:/bin/sh
Let’s take that password, which is probably crypt(), and run it through John the Ripper.
john --wordlist=/usr/share/wordlists/rockyou.txt ./etc/passwd
admin:wibble:101:101:Switch Administrator:/home/admin:/usr/local/bin/adminsh
cli:wibble:102:101:Switch Administrator CLI:/home/admin:/usr/local/bin/cfgcli
TMCTF:odagirih:0:0:Hold the backdoor:/home/admin:/bin/sh
sertest:NO PASSWORD:99:99:Factory Test:/:/usr/local/bin/loopsertest /dev/ttyS00
Hmm, let’s try TMCTF{odagirih}.
No luck with that, I wonder if the password was meant to be longer and it got truncated (DES uses a 56 bit key, where passwords are truncated to 8 characters and coerced into 7 bits each).
$ cat /usr/share/wordlists/rockyou.txt | grep odagirih
odagirihayato
Flag
TMCTF{odagirihayato}